What Is a JWT?
A JWT (JSON Web Token) is a type of token widely used in web development and APIs to securely transmit user information between a client and a server. If you are building an authentication system, you have almost certainly worked with JWT. To understand exactly how each part works under the hood, see our deep-dive on what actually happens inside a JWT.
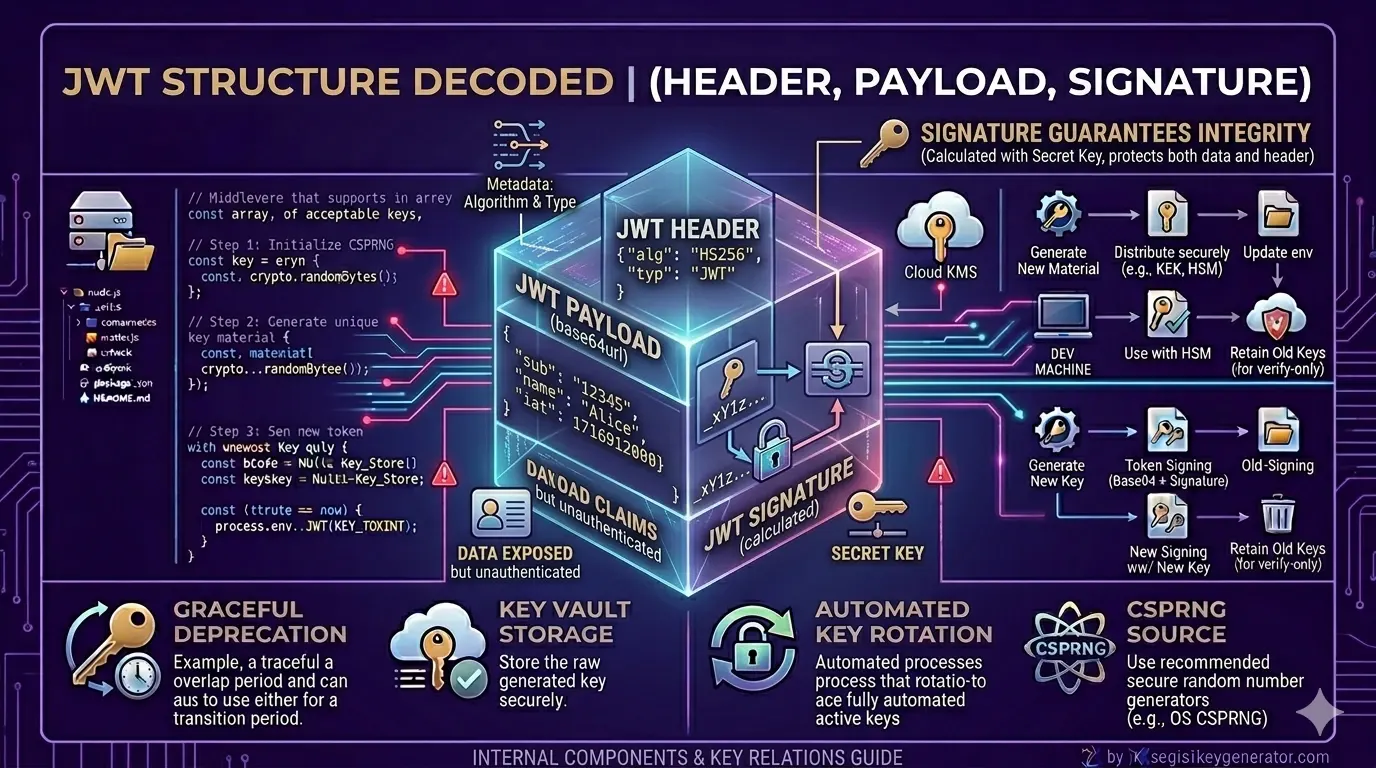
Every JWT is made up of exactly three parts, separated by dots:
xxxxx.yyyyy.zzzzz
Each part serves a very specific purpose:
| Part | What It Contains | Encoding |
|---|---|---|
| Header | Token type and signing algorithm (e.g. HS256) | Base64URL |
| Payload | User data — ID, role, email, expiry | Base64URL |
| Signature | Cryptographic proof of authenticity | HMAC / RSA signed |
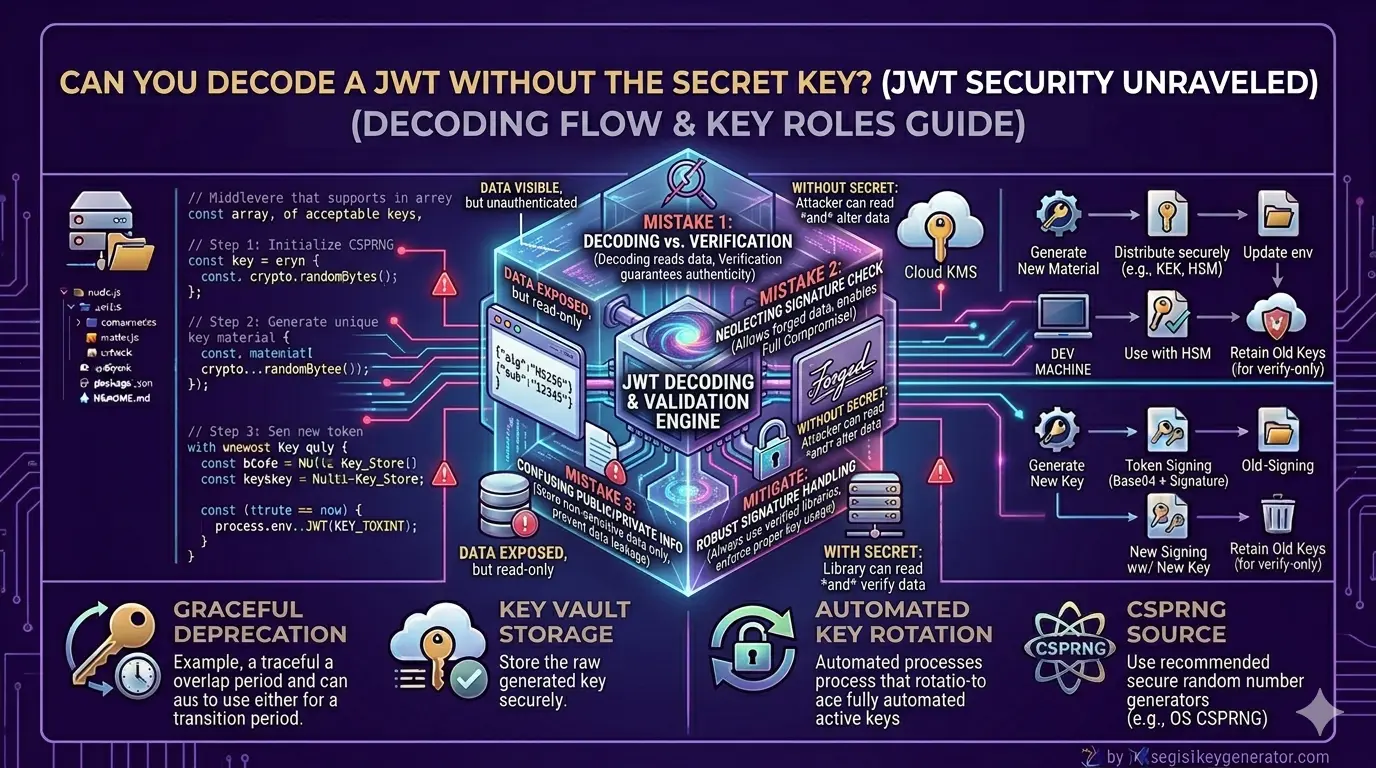
Is It Possible to Decode Without the Secret Key?
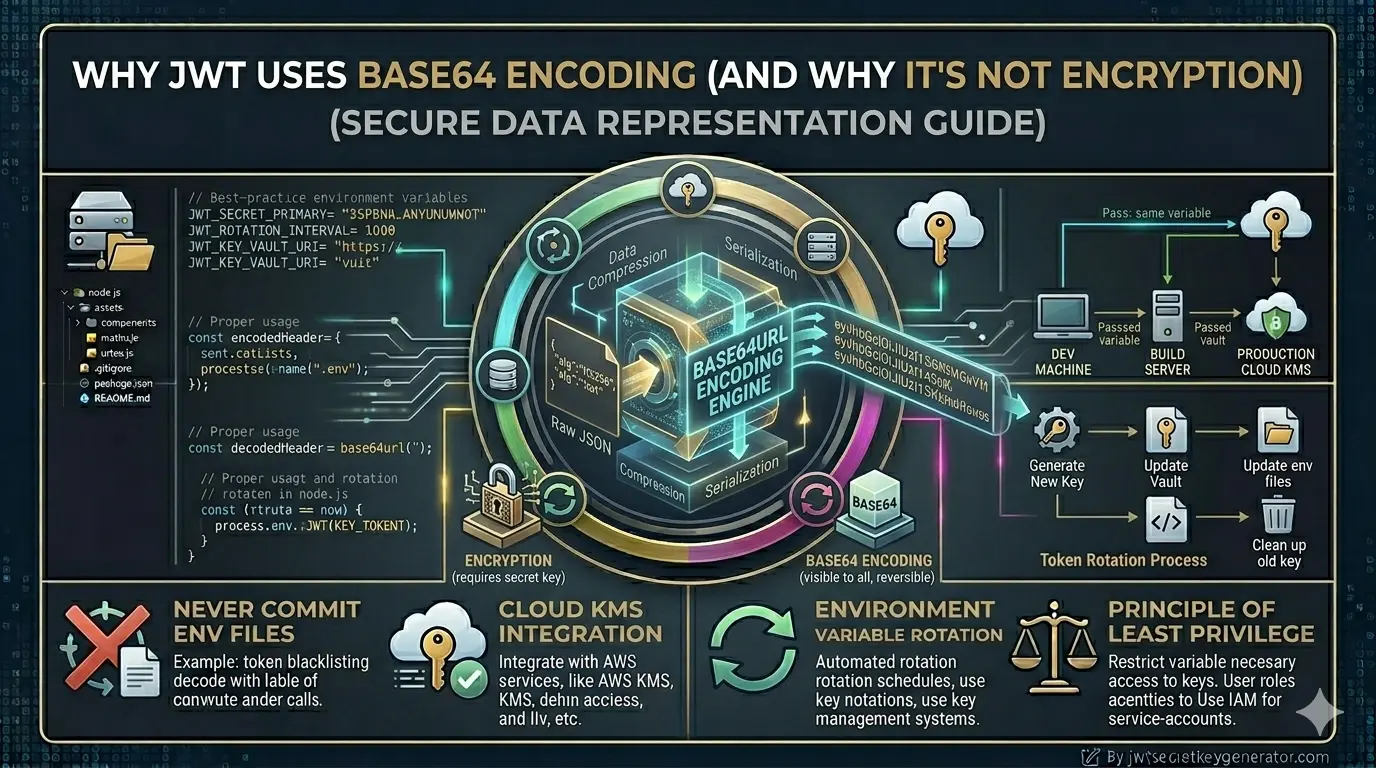
Yes — and this surprises most developers. You can absolutely decode a JWT and read its header and payload without knowing the secret key. No special tools, no hacking required. This works because the header and payload are only Base64URL encoded — not encrypted.
Encoding is not encryption. Base64 is a reversible transformation that anyone can undo in seconds using a simple online tool or a single line of JavaScript.
🔑 The Critical Distinction
Read the token's header and payload data. No secret key needed.
Confirm the token is authentic and untampered. Secret key required.
Without the secret key, you can read the data inside a JWT — but you have no way to confirm whether that data is real or has been altered by an attacker.
A Real-World Example
Imagine your server issues a JWT to a user after login. The payload inside looks like this:
{
"userId": 101,
"role": "admin",
"exp": 1746000000
}
Now, an attacker intercepts this token. They paste it into jwt.io — a completely free, public tool — and instantly read the payload. They can see the user ID, the role, and the expiry.
Here is the dangerous part — they now modify the payload, changing role: "user" to role: "admin". But they cannot recreate a valid signature without the secret key. So if your server always verifies the signature before trusting a token, their modified token will be rejected immediately.
Ways to Decode a JWT
Decoding a JWT is straightforward. Here are the three most common methods developers use:
- Online tools: Simply visit jwt.io, paste your token, and instantly see the decoded header and payload
- JavaScript
atob()function: Split the token by dots, take the second part (payload), and decode it usingatob()in any browser console - Backend libraries: In Node.js use
jsonwebtoken, in Python usePyJWT, in Java usejjwt— all support decoding without verification
// JavaScript — decode payload without secret key
const token = "your.jwt.token";
const payload = JSON.parse(atob(token.split('.')[1]));
console.log(payload); // readable data — no secret needed
Things to Keep in Mind
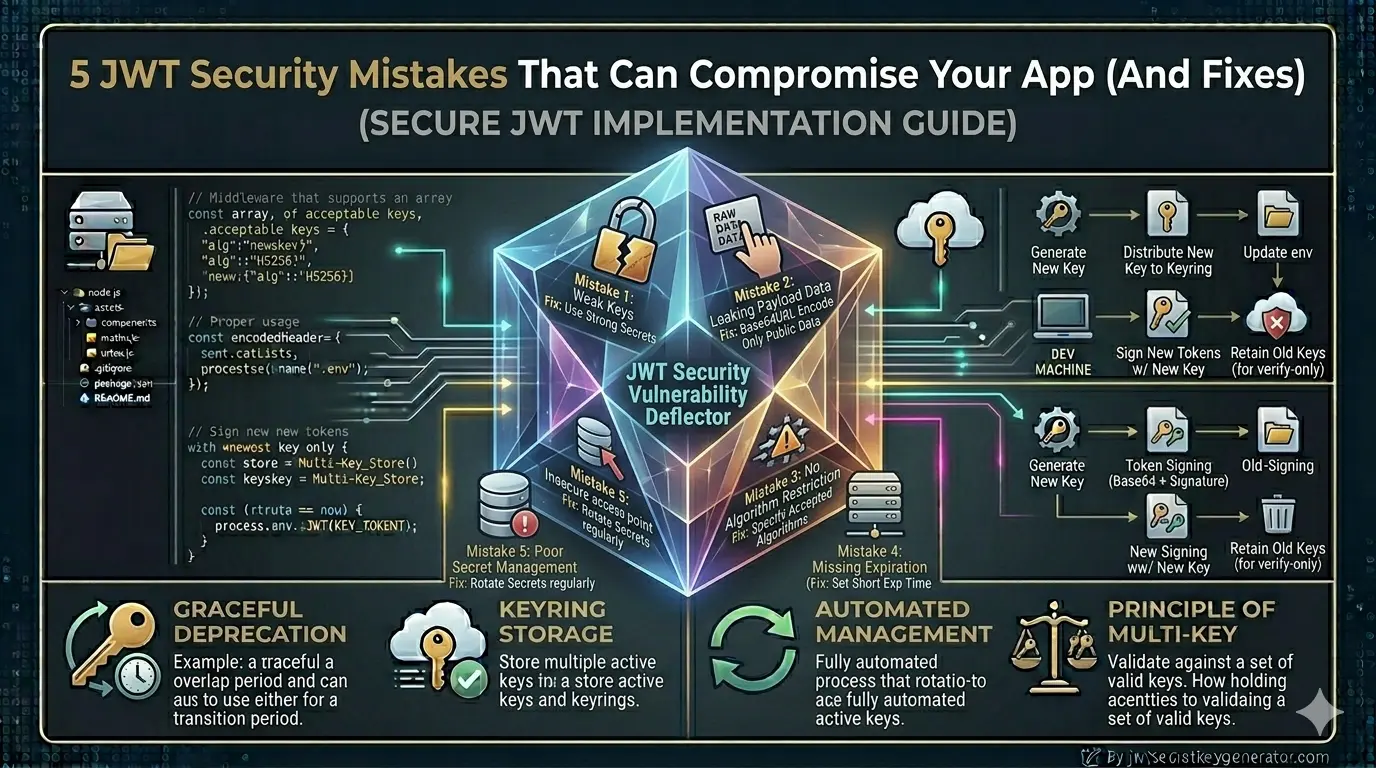
Now that you understand the difference between decoding and verifying, here are the security rules every developer must follow:
- Never store sensitive data in the payload: Passwords, credit card numbers, private keys — none of these belong in a JWT payload. Anyone who has the token can read it
- Decoded data is never automatically trusted: Just because you can read the payload does not mean the data is valid or unmodified
- Always verify the signature on the server side: Use
jwt.verify()in Node.js — never usejwt.decode()alone for authentication decisions - Use HTTPS always: Even though the payload can be decoded, transmitting tokens over HTTPS prevents interception during transit
| Action | Secret Key Needed? | Can Read Data? | Can Trust Data? |
|---|---|---|---|
| Decode JWT | No | Yes | No |
| Verify JWT | Yes | Yes | Yes |
The Bottom Line
Decoding a JWT without the secret key is completely possible — and it is by design, not a flaw. The header and payload are readable by anyone. The secret key's job is not to hide the data, but to prove the token's authenticity through its signature.
- Anyone can decode a JWT and read the header and payload — no secret key needed
- The signature verification always requires the secret key
- Never trust decoded data without verifying the signature first
- Never store sensitive information inside a JWT payload
- Always use
jwt.verify()— neverjwt.decode()— for authentication logic
🔐 Need a cryptographically secure JWT secret key? Generate a production-ready key instantly — free, browser-based, and never stored on any server.
Frequently Asked Questions
Can you decode a JWT without the secret key?
Yes, you can decode the header and payload of a JWT without the secret key because they are Base64-encoded, not encrypted. However, you cannot verify the signature without the secret key, which means you cannot confirm whether the token is authentic or has been tampered with.
What is the difference between decoding and verifying a JWT?
Decoding a JWT simply reads the header and payload data — no secret key required. Verifying a JWT checks the signature to confirm the token is authentic and untampered — this requires the secret key.
Is it safe to put sensitive data in a JWT payload?
No. Since the JWT payload can be decoded without any secret key using simple Base64 decoding, never store sensitive information like passwords, credit card numbers, or private keys inside a JWT payload.
How can I decode a JWT?
You can decode a JWT using online tools like jwt.io, using the JavaScript atob() function, or using backend libraries in Node.js, Python, or any other language. Remember that decoding only reads the data — it does not verify the token's authenticity.