All Articles
Everything you need to know about JWT secret keys, token security, authentication best practices, and Node.js implementation.

JWT Secret Key Best Practices (With Real Security Examples)
Read article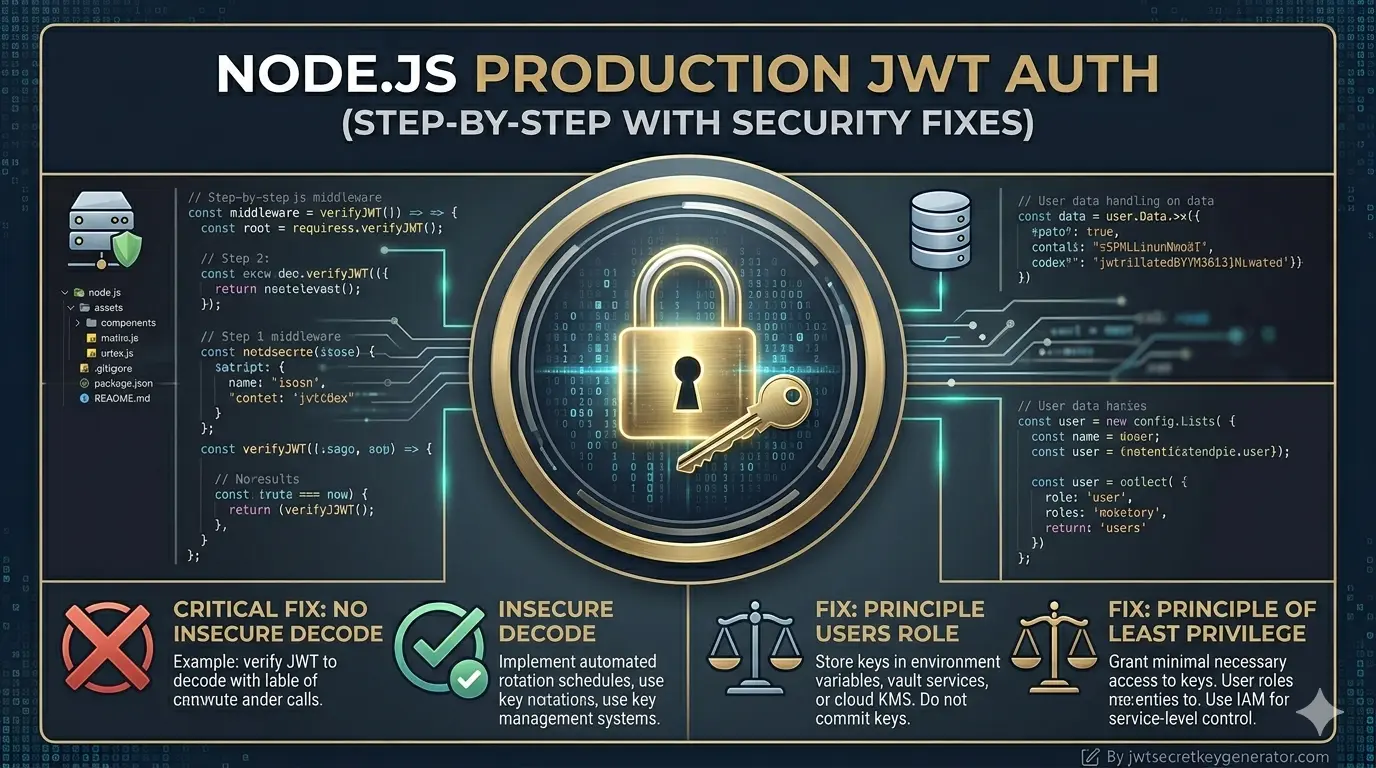
Production-Ready JWT Authentication in Node.js (Step-by-Step with Security Fixes)
Read article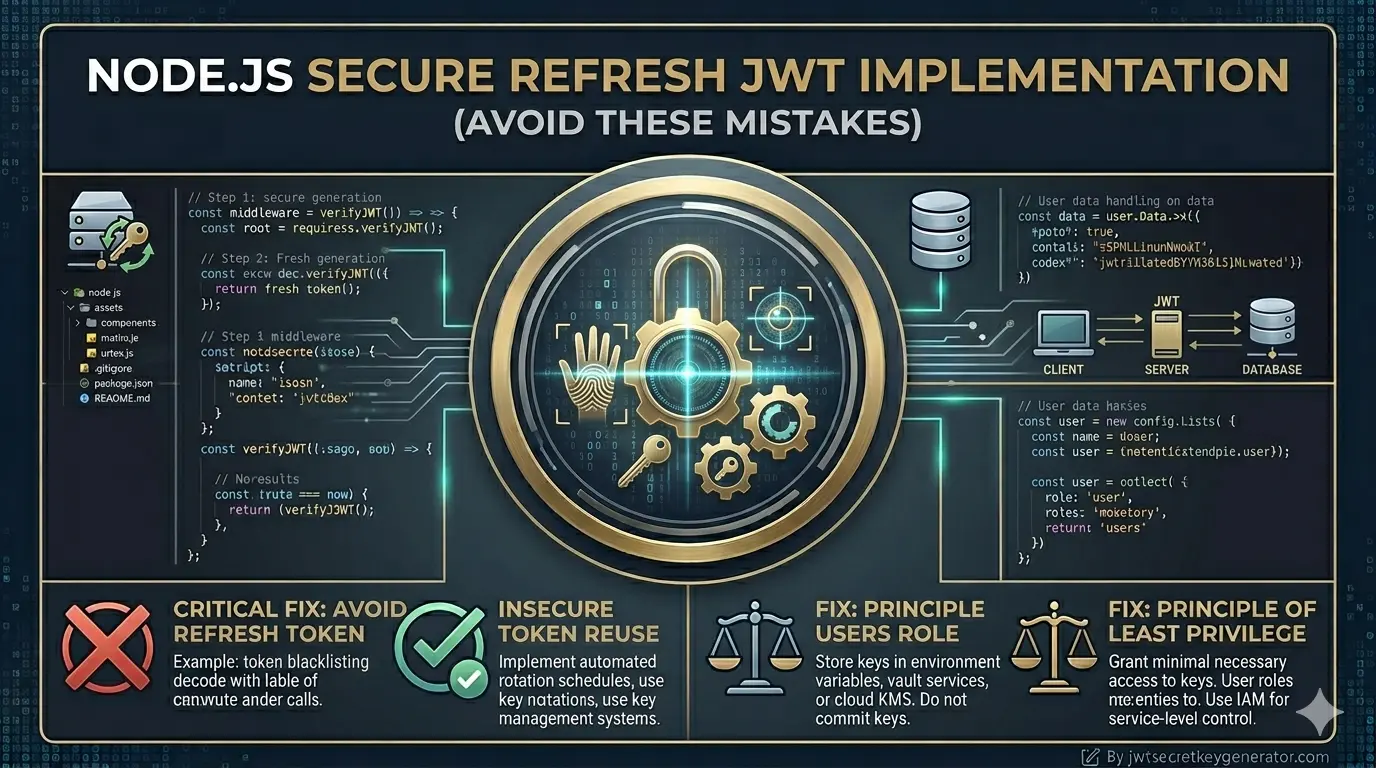
Secure JWT Refresh Token Implementation in Node.js (Avoid These Mistakes)
Read article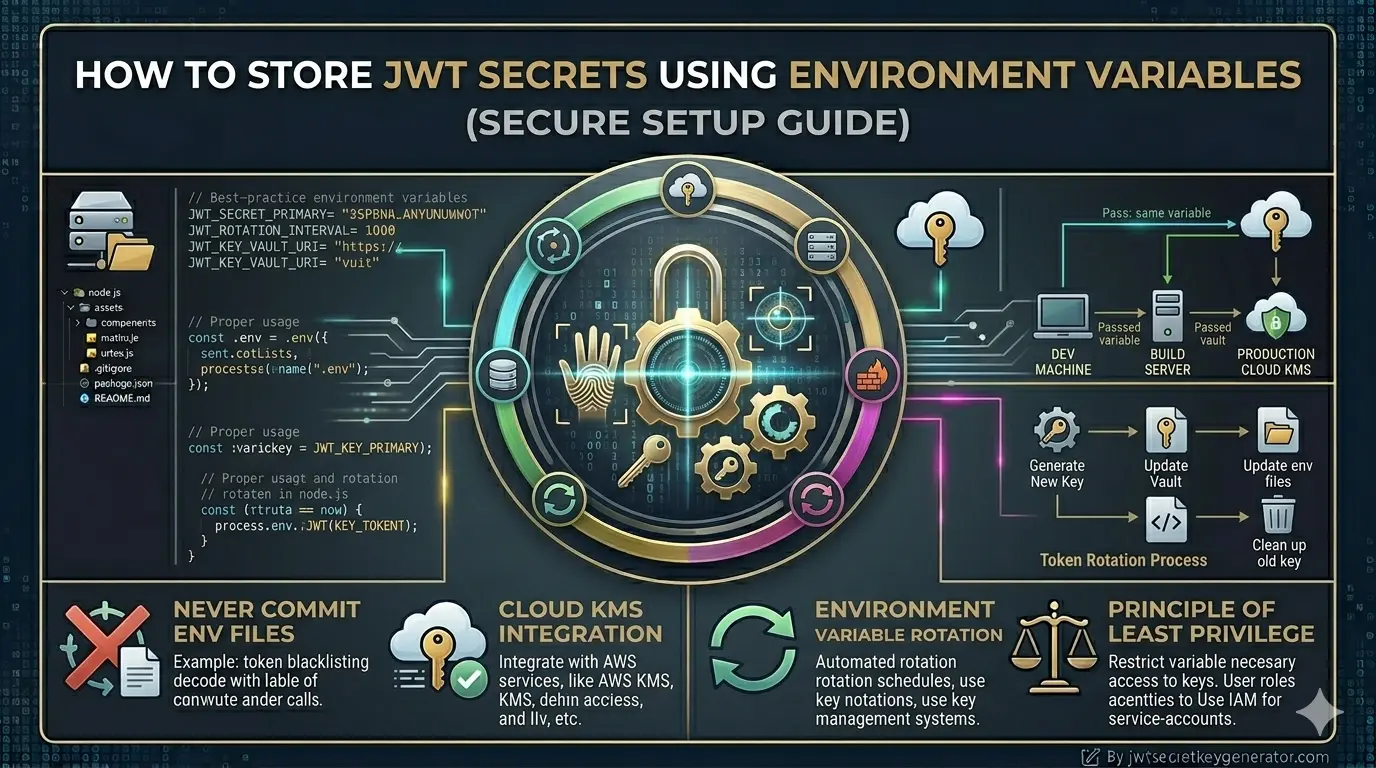
How to Store JWT Secrets Using Environment Variables (Secure Setup Guide)
Read article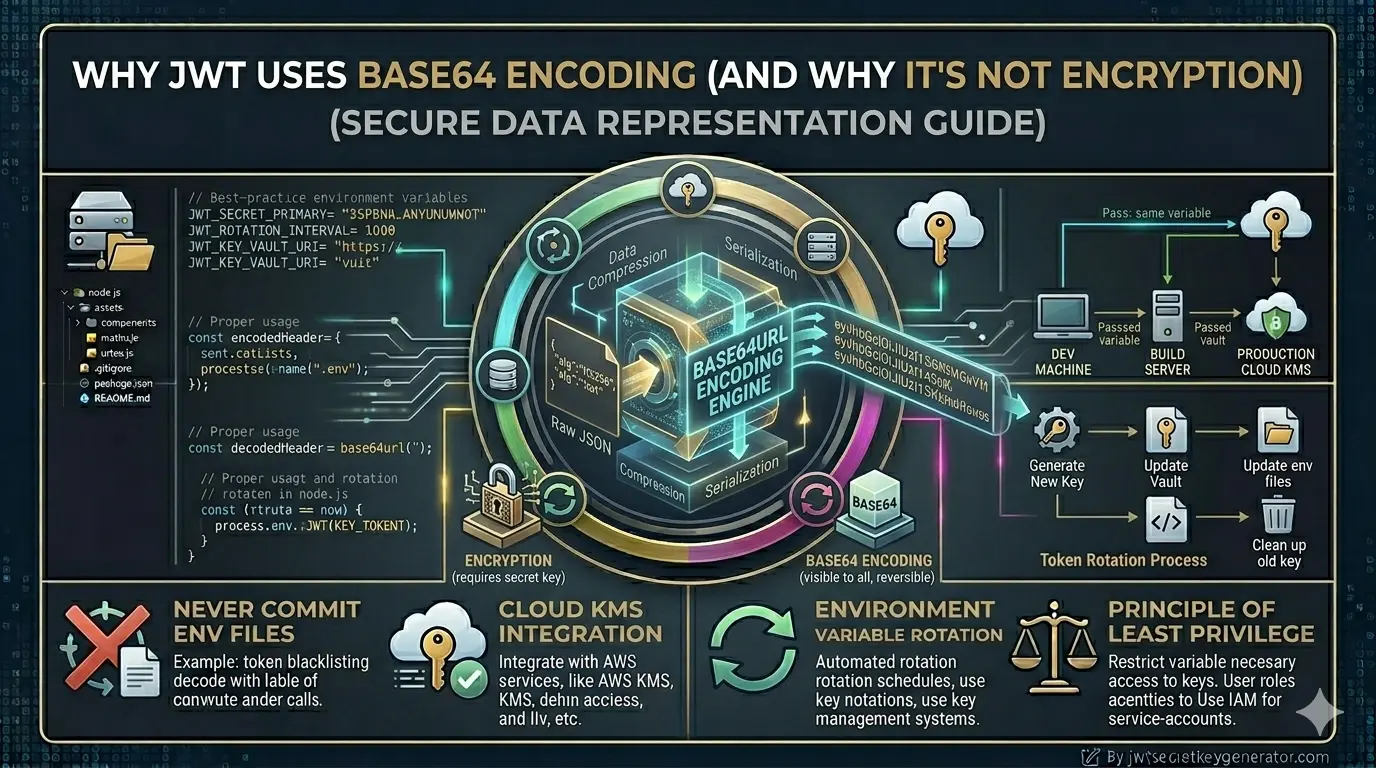
Why JWT Uses Base64 Encoding (And Why it's NOT Encryption)
Read article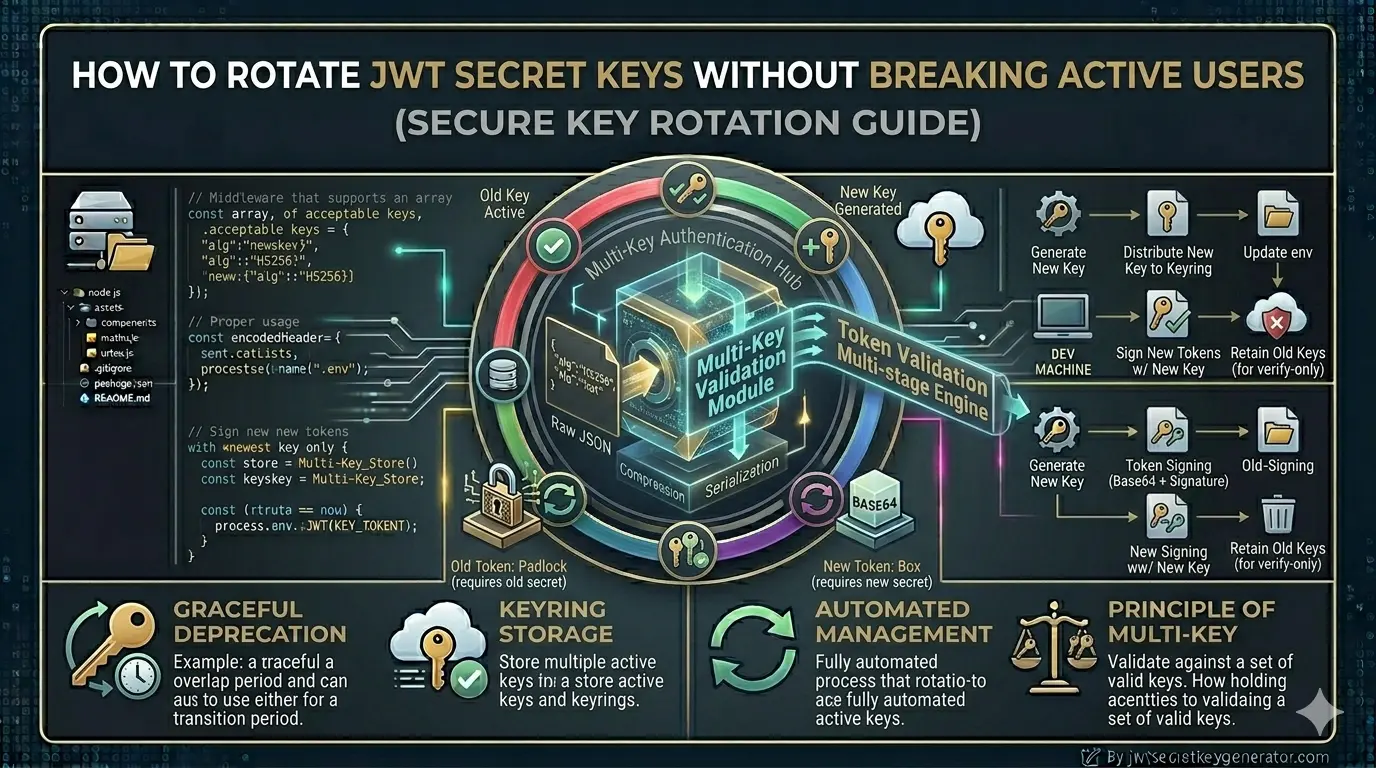
How to Rotate JWT Secret Keys Without Breaking Active Users
Read article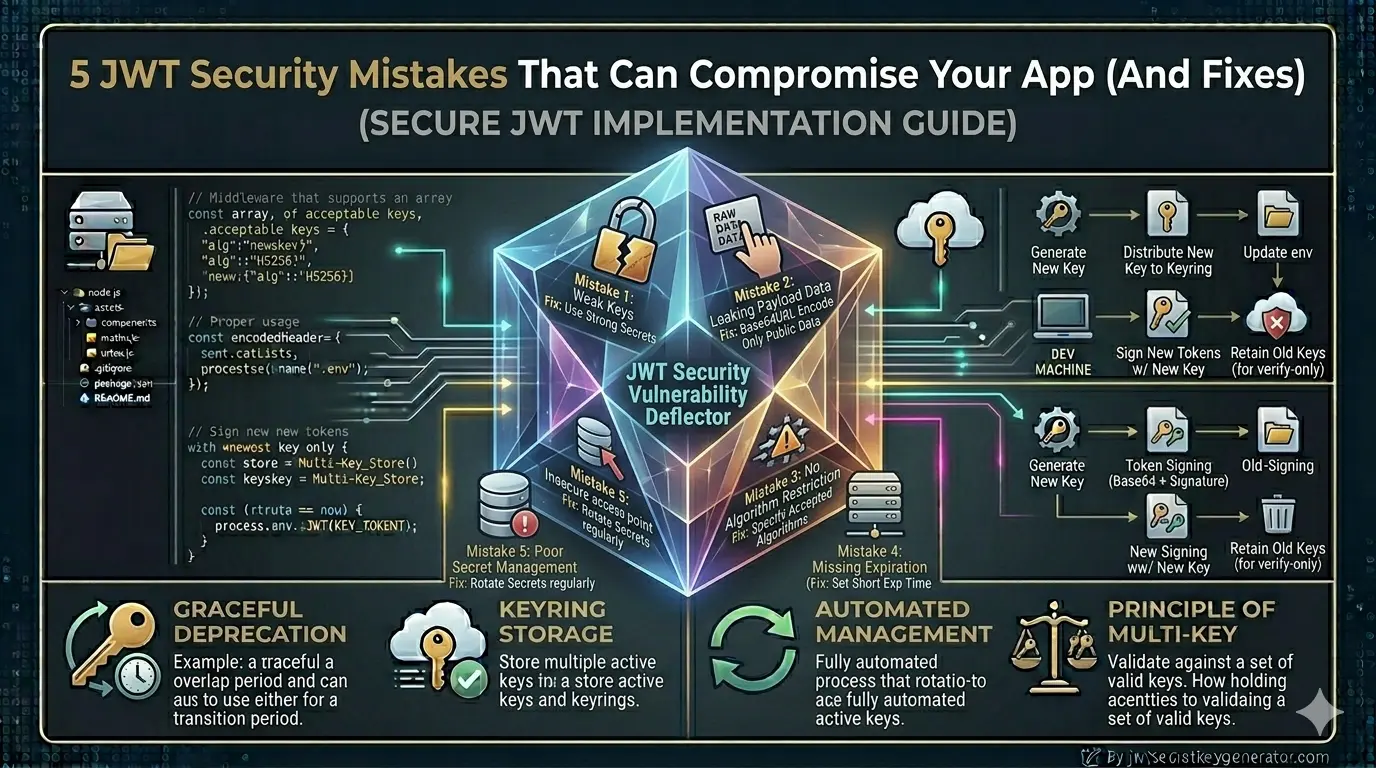
5 JWT Security Mistakes That Can Compromise Your App (And Fixes)
Read article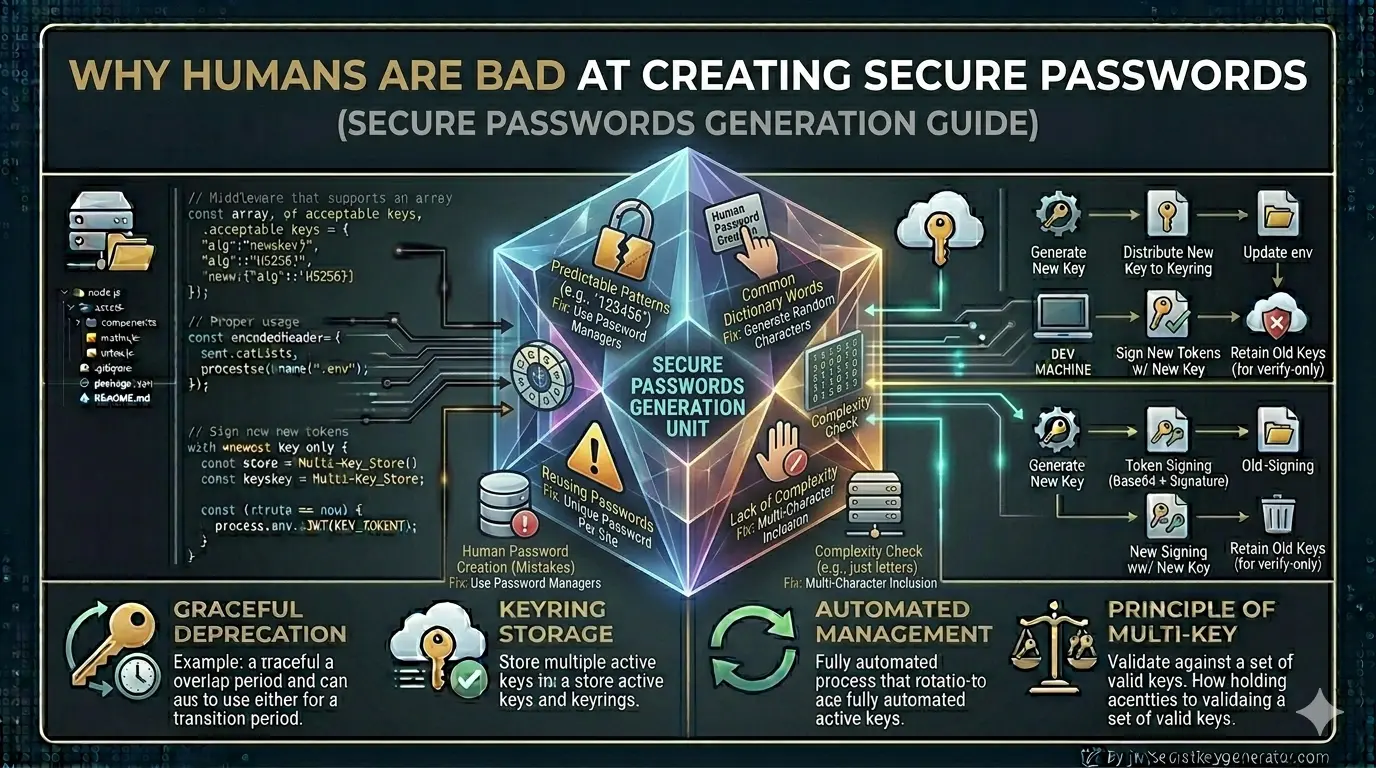
Why Humans Are Bad at Creating Secure Passwords (And What to Do Instead)
Read article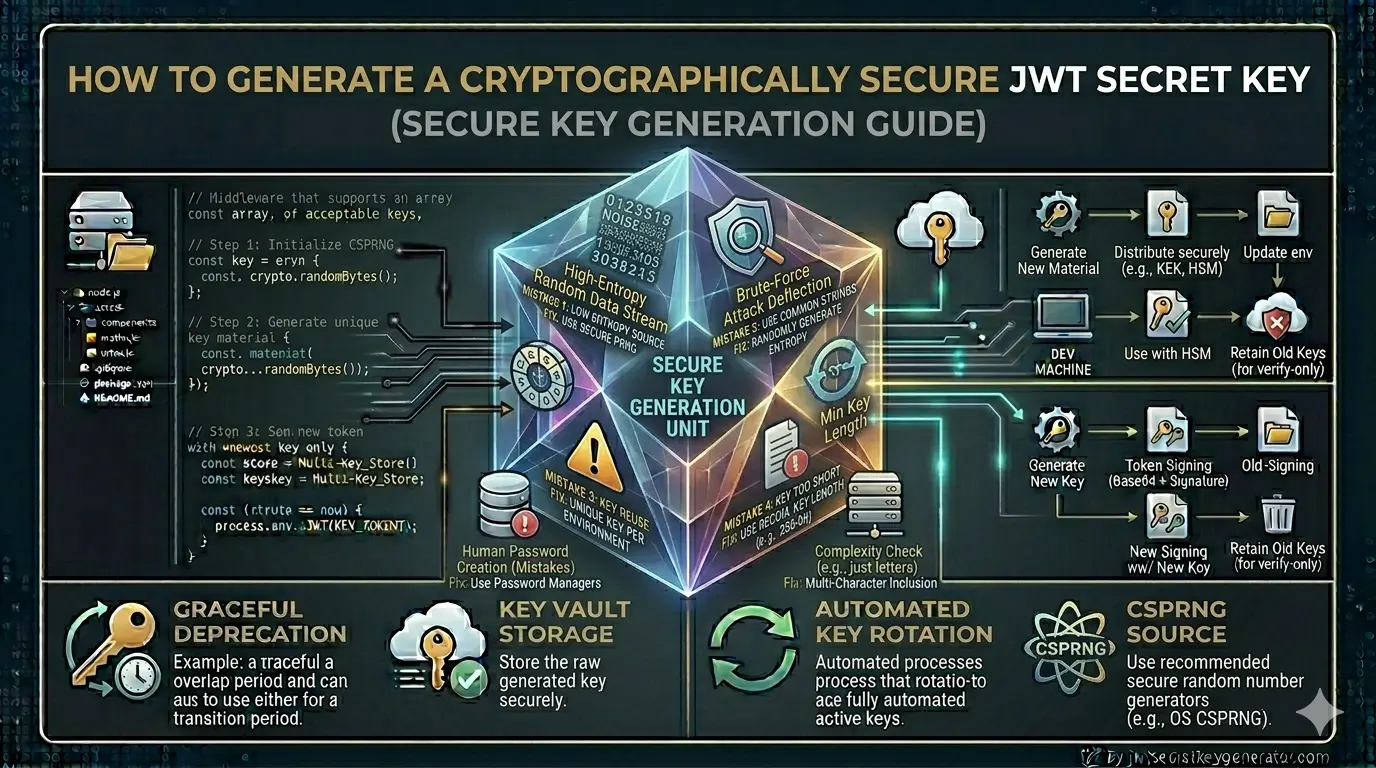
How to Generate a Cryptographically Secure JWT Secret Key
Read article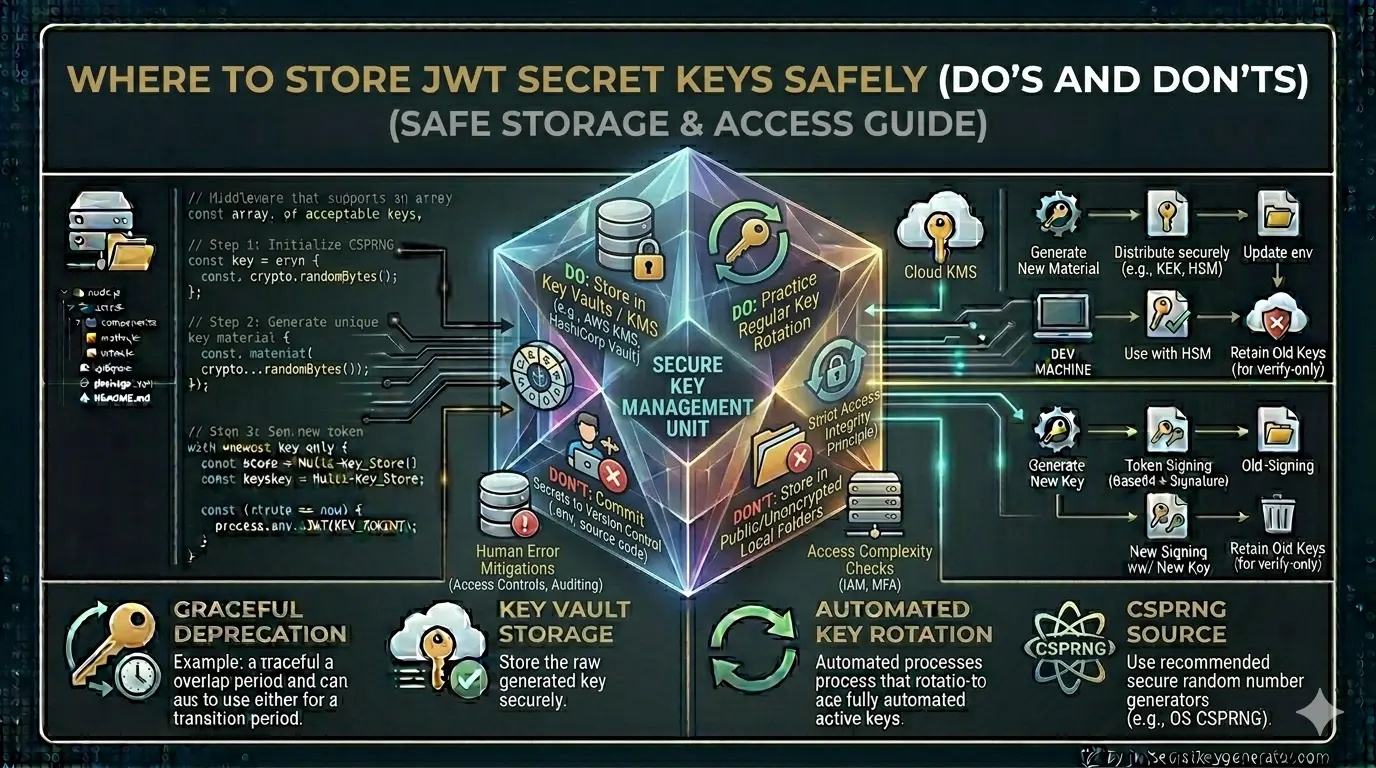
Where to Store JWT Secret Keys Safely (Do's and Don'ts)
Read article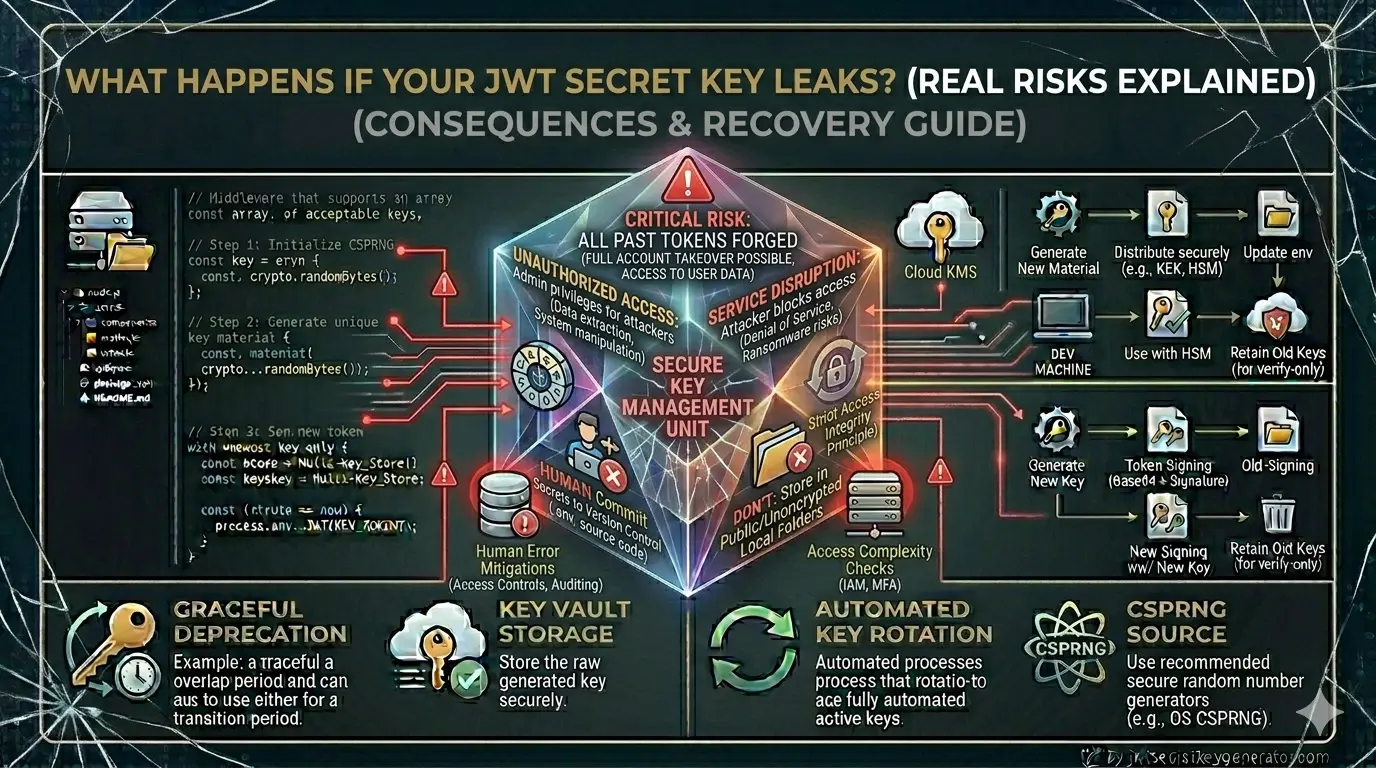
What Happens If Your JWT Secret Key Leaks? (Real Risks Explained)
Read article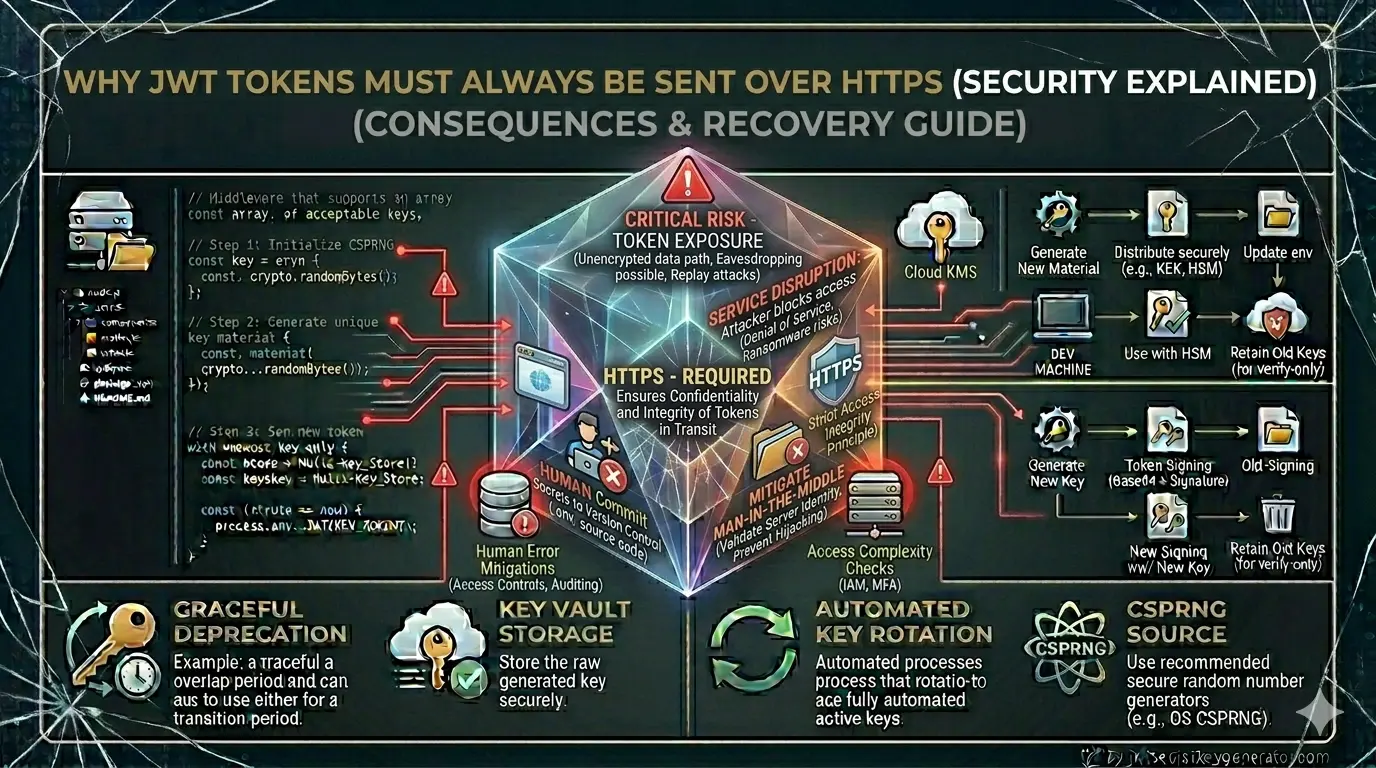
Why JWT Tokens Must Always Be Sent Over HTTPS (Security Explained)
Read article
Copied to clipboard!