What Does "Cryptographically Secure" Mean?
There is a critical difference between an ordinary random number and a cryptographically secure one.
- Follows a predictable pattern
- Generated from a seed value
- Can be reverse-engineered by attackers
- Completely unsuitable for security
- Uses OS-level entropy sources
/dev/urandom(Linux/macOS) orCryptGenRandom(Windows)- Truly unpredictable — no patterns
- Designed specifically for security
🔑 The JWT secret key must always be generated by a CSPRNG — never typed manually, never created with Math.random().
Weak Secret Keys — Never Use These
Before covering how to generate a good key, understand what not to do. All of the following can be guessed or broken by brute force:
❌ Manually typed: JWT_SECRET="mysecretkey"
❌ Math.random(): const s = Math.random().toString(36)
❌ Timestamp-based: const s = Date.now().toString()
❌ UUID-based: const s = uuid() // not designed for security
❌ Company/name-based: JWT_SECRET="MyCompanyName2024!"
Requirements for a Secure JWT Secret Key
HS256 → 256 bits (64 hex chars)
HS384 → 384 bits (96 hex chars)
HS512 → 512 bits (128 hex chars)
Generated exclusively by a CSPRNG — never by human input or Math.random()
No recognisable words, dates, or substitution tricks — pure entropy
Each application and each environment (dev/staging/prod) needs its own key
5 Methods to Generate a Secure Key
Online Tool — Fastest & Easiest
For a production-ready secure key without any terminal or code, use jwtsecretkeygenerator.com. It uses the Web Crypto API (a CSPRNG), runs entirely client-side — no data is ever sent to any server — and supports 256-bit, 384-bit, and 512-bit keys in both standard (alphanumeric) and enhanced (with special characters) formats.
.env file✅ A production-ready secure JWT secret key in under 10 seconds — no installation, no terminal, no code.
Node.js Built-in Crypto Module
Node.js's built-in crypto module uses OS-level entropy via /dev/urandom — it is a CSPRNG. Run this one-liner directly in your terminal:
# 256-bit key — one-liner terminal command
node -e "console.log(require('crypto').randomBytes(32).toString('hex'))"
# Output example:
# a3f9b2c1d4e5f6a7b8c9d0e1f2a3b4c5d6e7f8a9b0c1d2e3f4a5b6c7d8e9f0a1
Generate in different formats:
const crypto = require('crypto');
// Hex format (64 characters for 256-bit)
const hexKey = crypto.randomBytes(32).toString('hex');
console.log('HEX:', hexKey);
// Base64 format
const base64Key = crypto.randomBytes(32).toString('base64');
console.log('Base64:', base64Key);
// Base64url format (URL-safe, commonly used in JWT)
const base64urlKey = crypto.randomBytes(32).toString('base64url');
console.log('Base64url:', base64urlKey);
// 512-bit key for maximum security
const strongKey = crypto.randomBytes(64).toString('hex');
console.log('512-bit:', strongKey);
OpenSSL — Terminal Command
OpenSSL uses an OS-level entropy source and is cryptographically secure. Works on Linux, macOS, and Windows (via Git Bash).
# 256-bit hex key (recommended)
openssl rand -hex 32
# 512-bit hex key (maximum security)
openssl rand -hex 64
# Base64 format
openssl rand -base64 32
💡 OpenSSL draws from the operating system's entropy pool — the same source as /dev/urandom. The output is fully CSPRNG-compliant.
Python — secrets Module
Python's secrets module is specifically designed for cryptographic use cases. It uses os.urandom() internally — a CSPRNG.
import secrets
# 256-bit hex key
hex_key = secrets.token_hex(32)
print('HEX:', hex_key)
# 256-bit URL-safe Base64 key
urlsafe_key = secrets.token_urlsafe(32)
print('URL-safe:', urlsafe_key)
⚠️ Never use Python's random module for security keys. Only the secrets module is CSPRNG-backed.
Browser Console — No Tools Required
If you only have a browser (F12 → Console), the Web Crypto API is available and is a CSPRNG. Paste this snippet:
// Paste into browser console (F12 → Console tab)
const array = new Uint8Array(32); // 256-bit = 32 bytes
crypto.getRandomValues(array);
const key = Array.from(array)
.map(b => b.toString(16).padStart(2, '0'))
.join('');
console.log(key);
✅ crypto.getRandomValues() is the browser's CSPRNG — the exact same engine used by jwtsecretkeygenerator.com.
Store the Generated Key Properly
Generating the key securely is only half the job. How you store and use it matters just as much.
.env fileJWT_SECRET=a3f9b2c1d4e5f6a7b8c9d0e1f2a3b4c5d6e7f8a9b0c1d2e3f4a5b6c7d8e9f0a1
.env to .gitignore immediately.env
.env.local
.env.production
process.envrequire('dotenv').config();
const jwt = require('jsonwebtoken');
const token = jwt.sign(
{ userId: user._id, role: user.role },
process.env.JWT_SECRET,
{ expiresIn: '15m', algorithm: 'HS256' }
);
jwt.verify()const decoded = jwt.verify(token, process.env.JWT_SECRET, {
algorithms: ['HS256'] // Always explicit — prevents 'none' attack
});
Recommended Key Lengths by Algorithm
| Algorithm | Minimum Bits | Hex Characters | Use Case |
|---|---|---|---|
| HS256 | 256 bits (32 bytes) | 64 characters | ✅ Standard — most apps |
| HS384 | 384 bits (48 bytes) | 96 characters | 🔶 High-security apps |
| HS512 | 512 bits (64 bytes) | 128 characters | 🔴 Maximum security / enterprise |
HS256 with a 256-bit key is sufficient for most applications. Consider HS512 only for high-security or financial applications where the extra computation is justified.
Good Key vs Bad Key — Visual Example
A good key is at least 64 hex characters, contains no recognisable words, mixes letters and numbers with no visible pattern, and was generated by a CSPRNG.
Which Method Is Best for You?
jwtsecretkeygenerator.com — one click, done in 10 seconds
crypto.randomBytes(32).toString('hex') — built-in, no dependencies
openssl rand -hex 32 — available on Linux, macOS, Git Bash
HashiCorp Vault or AWS Secrets Manager — automated rotation with access control
🔑 All methods share one non-negotiable requirement: a CSPRNG must be used. Everything else is secondary.
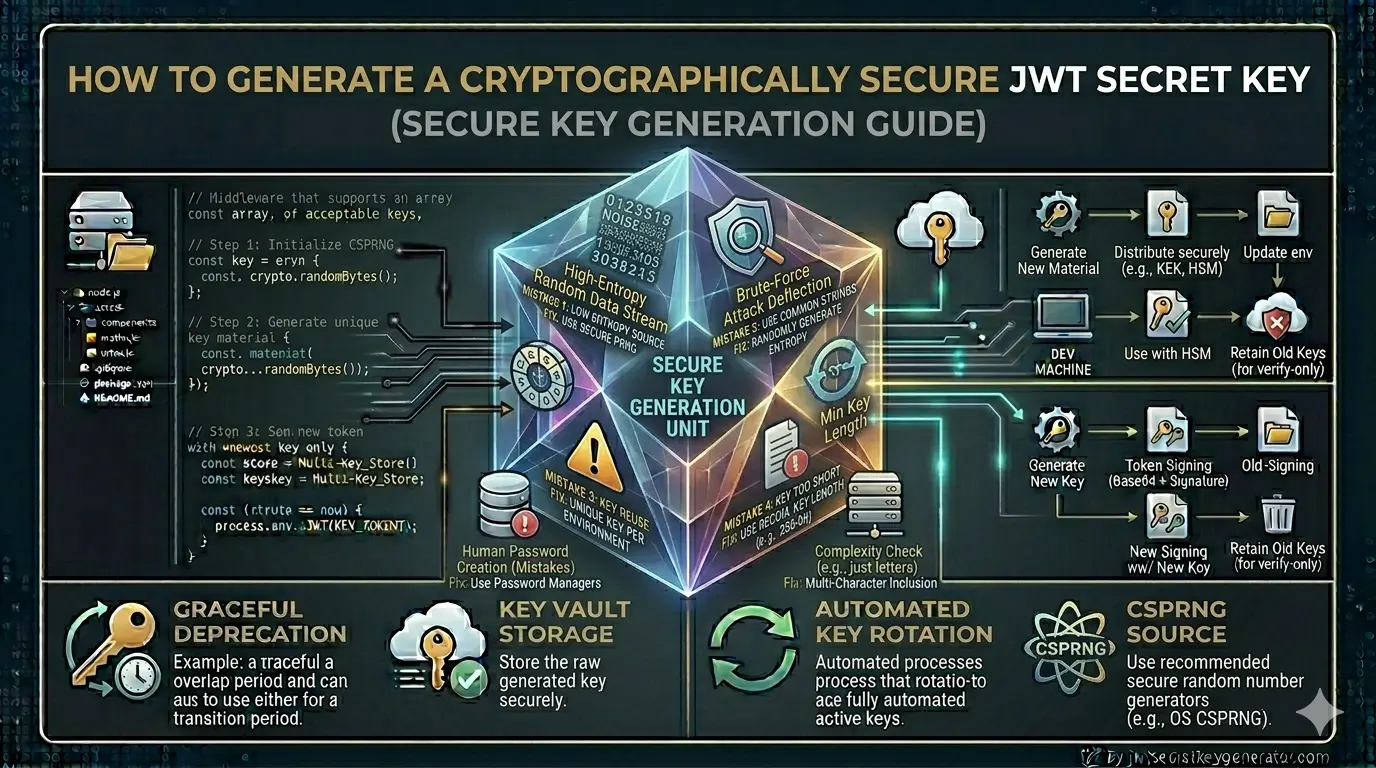
Common Key Generation Mistakes
crypto.randomBytes()
.env file — never in source code
Frequently Asked Questions
What is a cryptographically secure JWT secret key?
A cryptographically secure JWT secret key is one generated by a CSPRNG (Cryptographically Secure Pseudorandom Number Generator), such as Node.js crypto.randomBytes(), OpenSSL rand, Python secrets, or the browser Web Crypto API. It must be at least 256 bits (32 bytes / 64 hex characters) long, contain no recognizable patterns, and be unique per application.
Why can't I use Math.random() to generate a JWT secret key?
Math.random() is not cryptographically secure — it uses a predictable seed-based algorithm that experienced attackers can reverse-engineer. JWT secret keys must use a CSPRNG such as Node.js crypto.randomBytes(), which draws entropy from the operating system (/dev/urandom on Linux/macOS).
How long should a JWT secret key be?
The minimum recommended length depends on the algorithm: HS256 requires at least 256 bits (64 hex characters), HS384 requires 384 bits (96 hex characters), and HS512 requires 512 bits (128 hex characters). For most applications, a 256-bit key with HS256 provides sufficient security.
What is the fastest way to generate a secure JWT secret key?
The fastest way is to use jwtsecretkeygenerator.com — a free, browser-based tool that uses the Web Crypto API (CSPRNG) and generates a production-ready key in one click without sending any data to a server.
Conclusion
Generating a cryptographically secure JWT secret key isn't difficult — you just need to use the right method. The easiest and fastest approach is jwtsecretkeygenerator.com — one click and you have a CSPRNG-based, production-ready key. For code-based generation, Node.js's crypto.randomBytes() or openssl rand -hex 32 are the most reliable options.
🔑 The rule is simple: CSPRNG-generated + at least 256-bit + stored in .env + never committed to version control. Everything else is secondary.